SERVICE DESIGN & PRODUCT MANAGEMENT·GUSTO
Eliminating social engineering attacks on Gusto's customer support line.
TL;DR
A fraudster called Gusto support, passed verification, and stole money from a customer's account. We were assembled from three different teams to fix it in seven weeks.
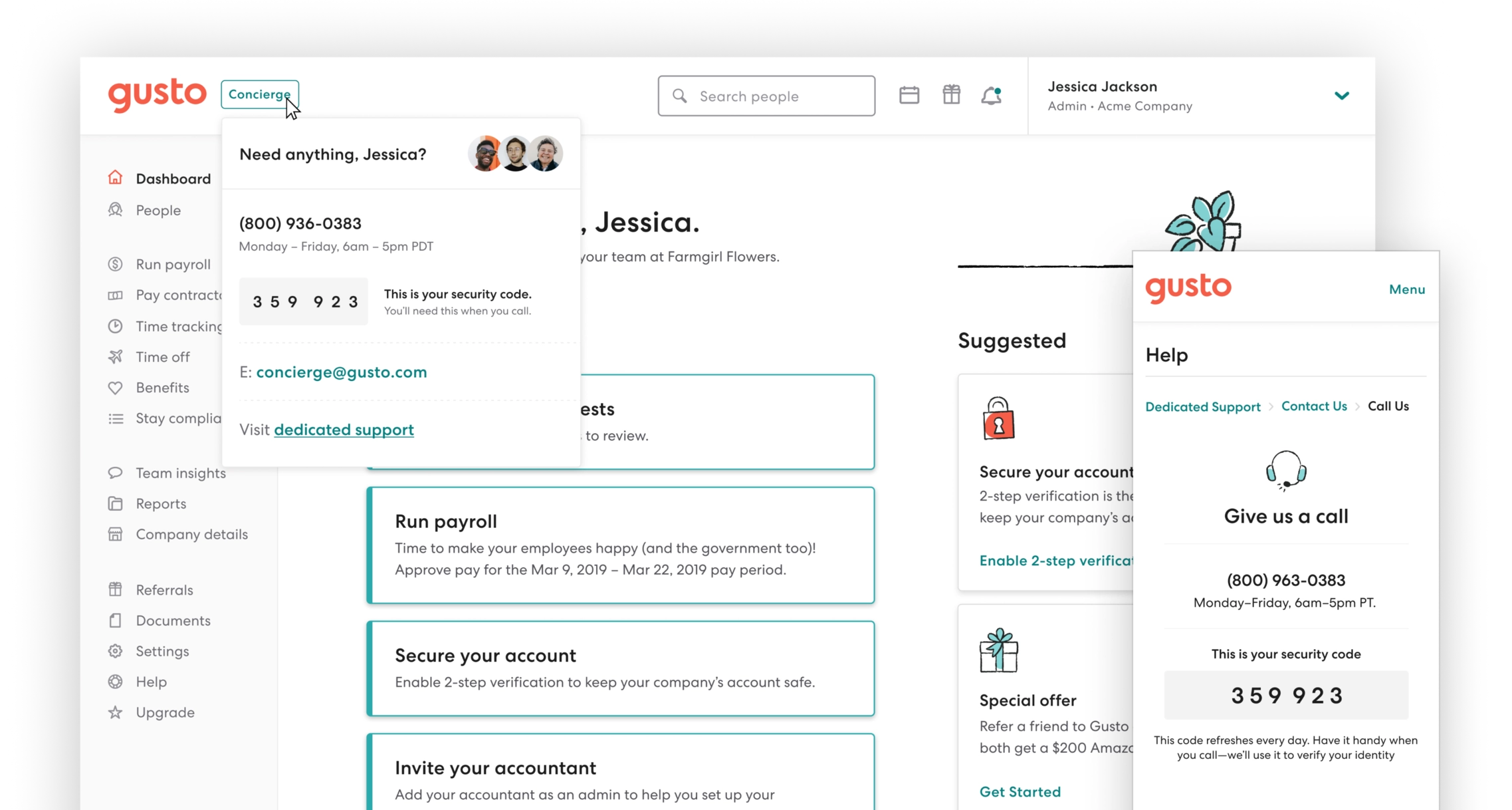
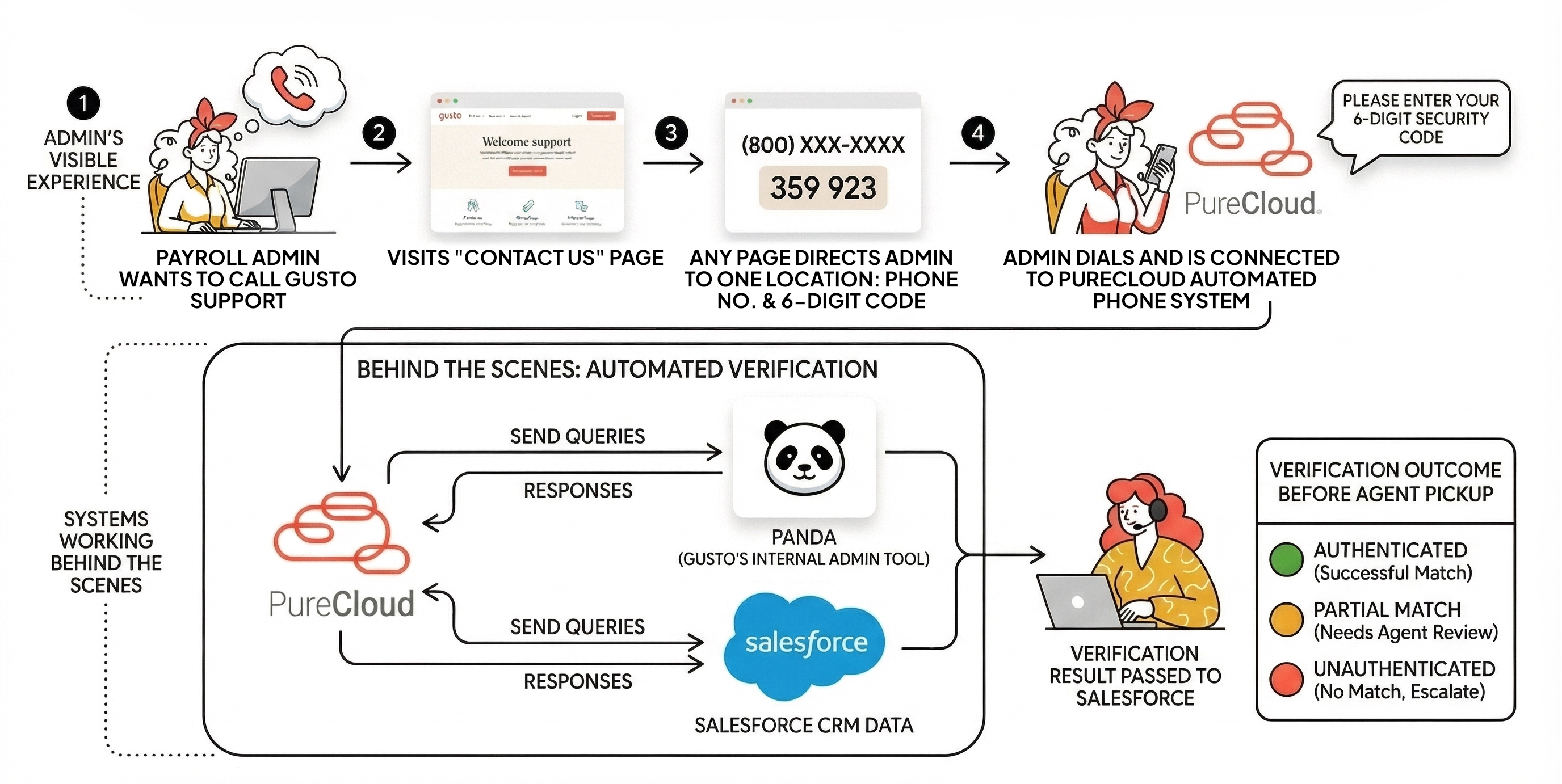
We studied five fintechs first, chose a design principle, and built every prototype around real callers — their actual company, their actual starting point. Not simulations. The fix: a 6-digit security code generated in the Gusto app, entered via phone before reaching a customer service agent.
- Zero social engineering attacks post-launch
- 95.1% first-attempt code accuracy — we'd aimed for 90%
- No negative impact on CSAT or CES
- Customer service teams saved 15 seconds per call × 100K calls/month
Fraudsters were calling support, passing verification, and stealing from customers.
A fraudster called Gusto support, passed our verification process, and stole money from a small business owner's account. Think about what that means — seeing your savings gone, knowing it happened through a vendor you trusted.
For Gusto: direct financial loss, recovery costs, potential reputation damage. We needed to fix this fast.
The verification questions — full name, date of birth, last four of SSN — were no longer secure after the Equifax breach. There was no unified strategy across care teams. And calls transferred from sales or third-party partners bypassed verification entirely.
Eight of us were pulled from three different orgs — I was the only designer and also took on product management duties. We had seven weeks, and only one of us had a security background.
Five fintechs were solving this differently. We chose high security, low friction for users — high friction for fraudsters.
Before sketching anything, we interviewed five fintech startups who were also trying to solve this problem. What emerged was a clear design principle: make it easy for legitimate users, hard for fraudsters.
The solution: a unique 6-digit security code in the Gusto app, entered via the phone before reaching an agent. A fraudster without account access couldn't get it.
We ran two research streams in parallel. First, we partnered with the care team to ask every caller three questions for two weeks — where did you find the phone number, are you logged in, are you near your computer?
We also dug into our data, which surfaced two distinct caller types: one-off callers (82% of volume) and frequent callers (18%), each with very different challenges.
From there, we ran 10 moderated testing sessions with people who had called Gusto within the previous two weeks to keep our sessions grounded in real-world scenarios.
Each prototype used the caller's real company, real context, real starting point.
This is the thing I'm most proud of in this project.
Each prototype was built around the specific person in front of us — their company name, their employee count, their actual location in the Gusto app. When they walked into the test, it felt like their actual life, not a simulation.
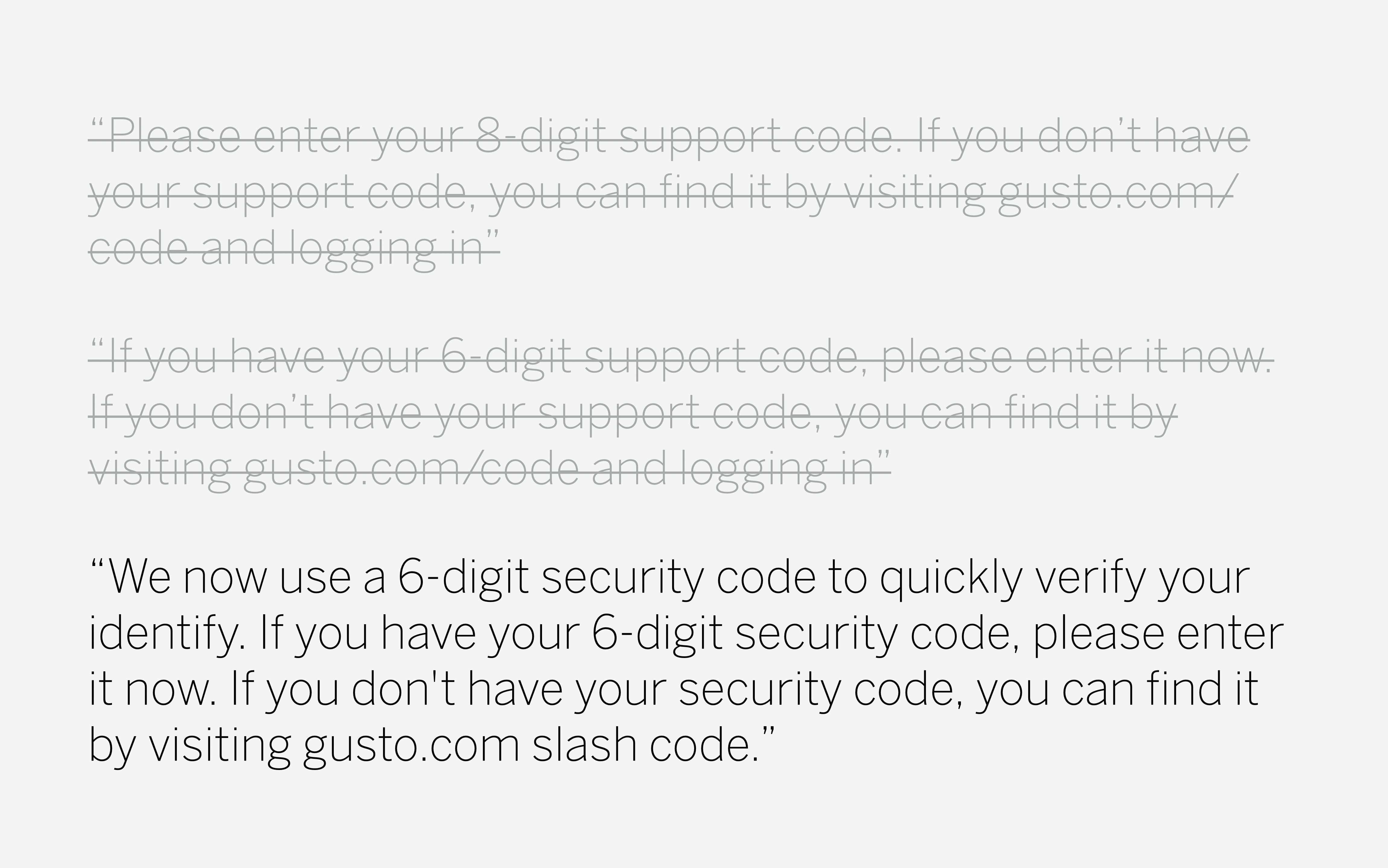
The interactive voice response (IVR) script went through three versions based on live feedback, and we iterated on the language until it felt clear and natural rather than confusing.
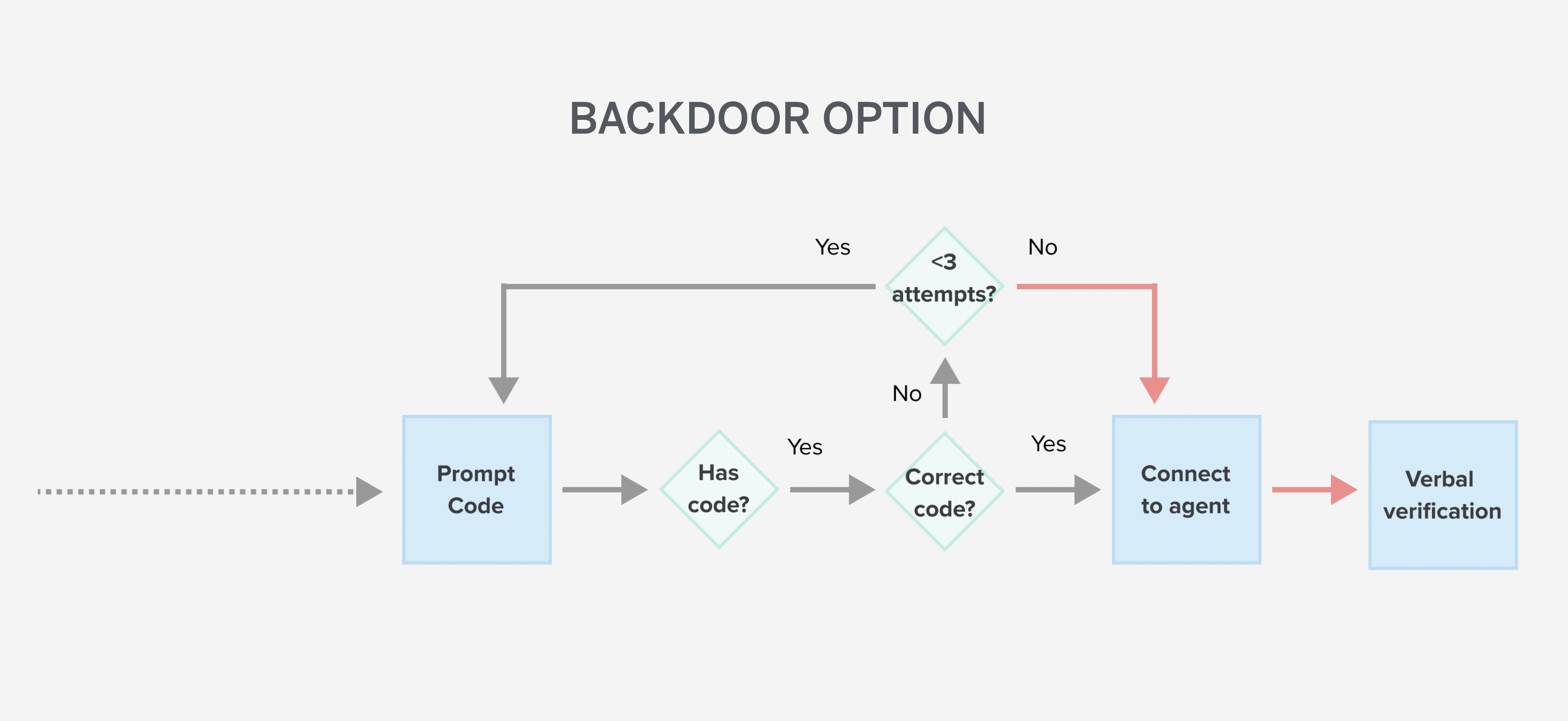
We also designed a secure backdoor for callers who genuinely couldn't access the app — higher friction questions that only the small business owner could answer, so it wouldn't become an easy path for fraudsters.
Callers noticed.
You guys have to verify I am who I am. There's this weird dance that I haven't gotten used to — do I say hello and four digits of my social? So, I like this [security code] better than always having to give my social [security] information.
Susan H, Noble Kinsman Brewing
Previously I'd need to confirm EIN every time. But if this is linked to my account and knows I'm Ian — that's pretty cool.
Ian S, Solistice
We piloted with 1,500 customers before full launch.
Zero attacks. 95.1% first-attempt accuracy. No negative impact on satisfaction.
The goal was 90% first-attempt accuracy — customers entering their security code before reaching an agent. We hit 95.1%.
Zero social engineering attacks post-launch, no negative CSAT or CES impact, and care teams saved 15 seconds per call — across 100,000 calls a month, that adds up.
The solution unified the experience across five platforms with no loopholes.